Got IT issues slowing you down? We provide both on-site and remote support across Australia, so help is never far away.
In today's digital landscape, data is the lifeblood of your business. A robust data backup strategy is no longer optional — it's a necessity. Whether it's a cyberattack, system failure, or accidental deletion, the ability to recover your data swiftly can mean the difference between business continuity and costly downtime.
This guide will walk you through the essential components of a reliable backup and recovery plan, tailored for small and medium-sized businesses. From understanding the 3-2-1 backup rule to implementing automated solutions, we've got you covered.
The 3-2-1 backup strategy is a time-tested approach to data protection:
Implementing this rule helps safeguard against various threats, ensuring that your data is always recoverable.
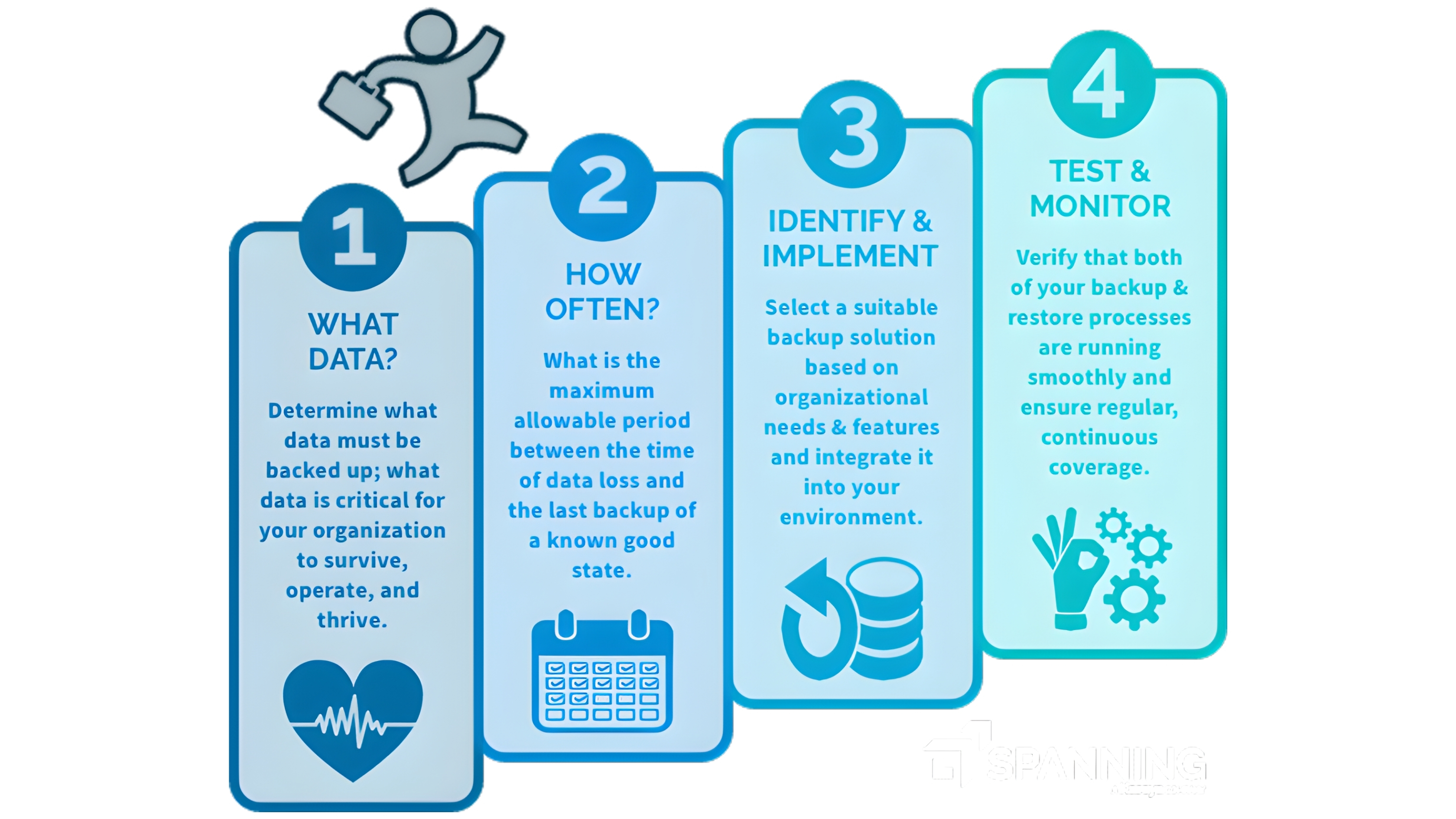
Manual backups are prone to human error and inconsistency. Automating your backup process ensures regular and reliable data protection. Consider the following steps:
Automation not only saves time but also reduces the risk of data loss due to overlooked backups.
Cloud backup offers scalability and remote access to your data. By integrating cloud solutions, you can:
Popular cloud backup providers include Google Drive, Microsoft OneDrive, and Dropbox. Ensure that the chosen provider aligns with your business's security and compliance requirements.
A backup is only as good as its ability to restore data. Regularly test your backups to ensure they are functional:
Regular testing ensures that your backup strategy remains effective and reliable.
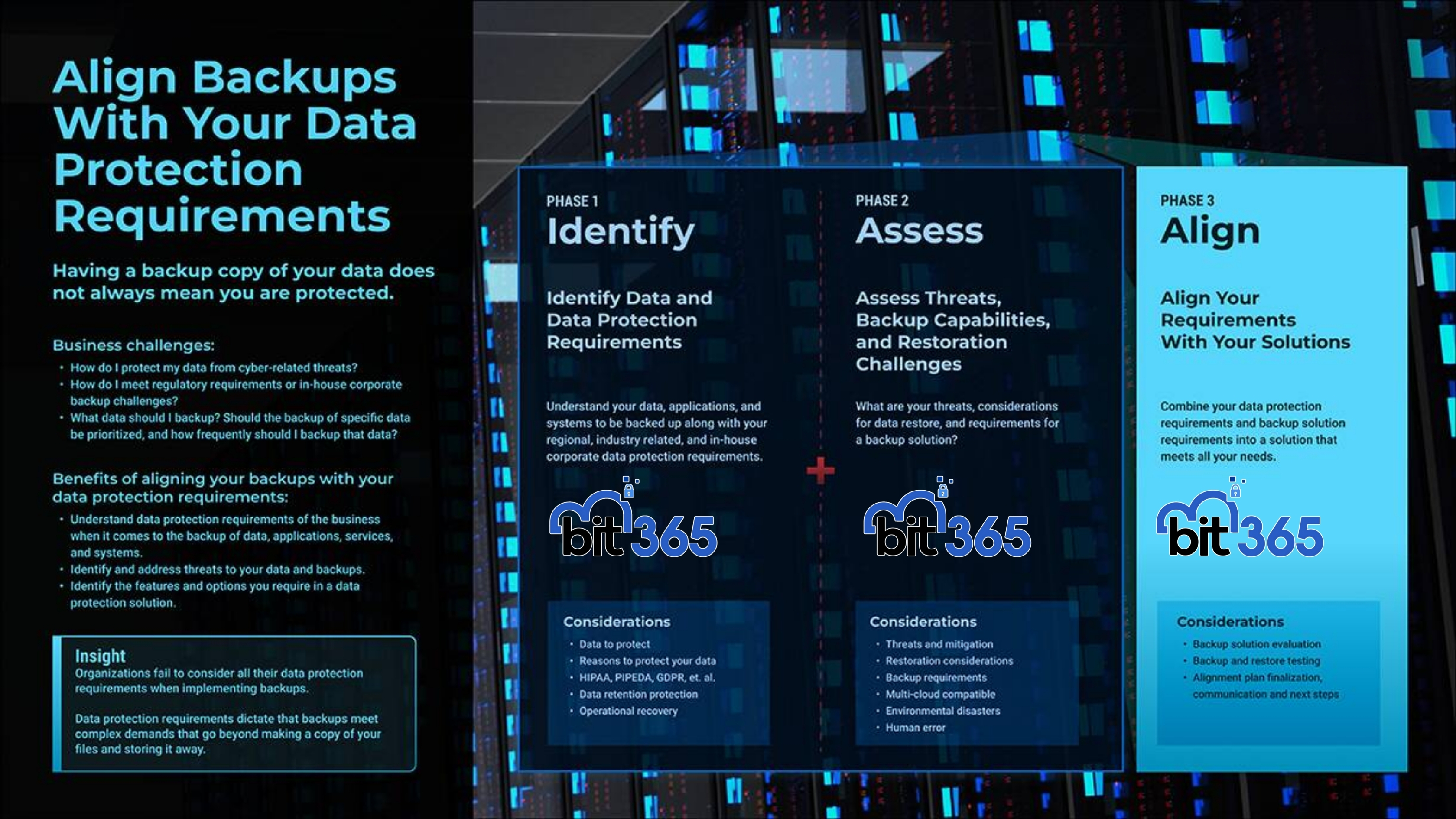
To create a comprehensive data backup strategy:
By following these steps, you can establish a robust data backup strategy that ensures business continuity and data security.
Challenge 1: Inconsistent backup schedules leading to potential data loss.
BIT365 Solution: Implement automated backup solutions with scheduled intervals to ensure regular data protection.
Challenge 2: Lack of off-site backups exposing data to local disasters.
BIT365 Solution: Adopt the 3-2-1 backup strategy, incorporating cloud storage as an off-site solution.
Challenge 3: Unverified backups causing delays during data recovery.
BIT365 Solution: Regularly test and verify backups to ensure quick and reliable data restoration.
Challenge 4: Limited scalability of backup solutions hindering business growth.
BIT365 Solution: Choose scalable cloud backup solutions that grow with your business needs.
Challenge 5: Lack of employee awareness leading to accidental data loss.
BIT365 Solution: Conduct regular training sessions to educate employees on data protection best practices.
Whether you're upgrading systems, improving security, or streamlining your IT setup, BIT365 can help. Contact us today and let’s make your technology work smarter for your people.
Got IT issues slowing you down? We provide both on-site and remote support across Australia, so help is never far away.
BIT365 offers a full range of managed IT services, including cybersecurity, cloud solutions, Microsoft 365 support, data backup, and on-site or remote tech support for businesses across Australia.
No. While we have a strong presence in Western Sydney, BIT365 supports businesses nationwide — delivering reliable IT solutions both remotely and on-site.
We pride ourselves on fast response times. With remote access tools and on-site technicians, BIT365 can often resolve issues the same day, keeping your business running smoothly.
BIT365 combines local expertise with enterprise-grade solutions. We’re proactive, not just reactive — preventing issues before they impact your business. Plus, our friendly team explains IT in plain English, so you always know what’s happening.
